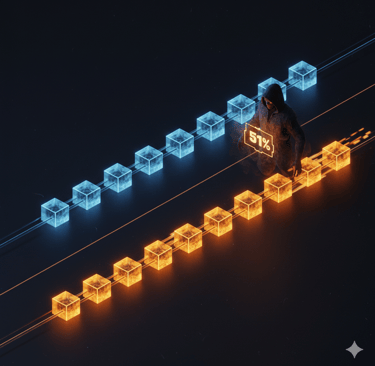
What is a 51% attack?
The $18 Million Ghost: Why Your Blockchain Isn't as Unstoppable as You Think
AI
Scott Barron
2/20/20265 min read

Introduction: The Bank Vault Illusion
In the physical world, robbing a bank is a matter of brute force: you need to crack the safe or bypass the laser grid. The vault is the target. But in the architecture of the blockchain, the vault is a red herring. To steal the money, you don’t break into the ledger; you simply take control of the computers that write it.
We are told that decentralization is a perfect, immutable shield. But that "immutability" is actually a consensus—a collective agreement on the truth. If a single entity controls more than 51% of the network’s power, they don’t just participate in the truth; they dictate it. This is the 51% attack, a mathematical exploit that proves that in a decentralized world, might doesn't just make right—it makes history.
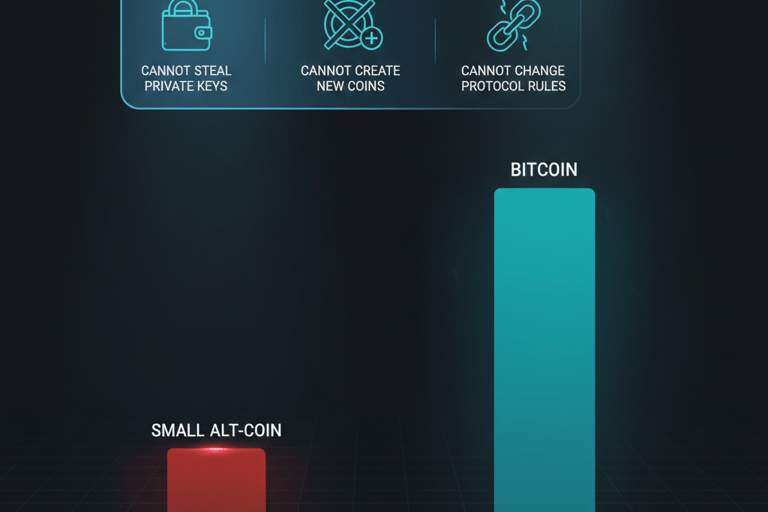
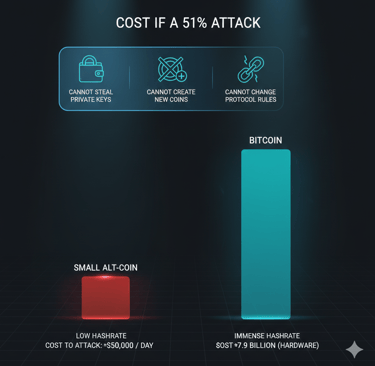
Takeaway 1: Security is an Expensive Electricity Bill (The Economic Barrier)
The security of a titan like Bitcoin isn't a result of "unbreakable" software. It is a moat built from sheer economic irrationality. The network is secure because attacking it is so prohibitively expensive that it becomes a financial suicide pact.
To seize 51% control of the Bitcoin network today, an attacker would need to spend approximately $7.9 billion on ASIC (Application-Specific Integrated Circuit) hardware alone. That doesn’t include the ongoing power bill: Bitcoin consumes roughly 120 terawatt-hours of electricity annually—a footprint comparable to the entire nation of Argentina. While Bitcoin sits behind this multi-billion dollar wall of silicon and heat, its security is defined by its scale.
"51% attacks represent the fundamental trade-off between decentralization and security. As networks grow more distributed, attacks become exponentially more expensive. The security of major networks like Bitcoin comes not from immunity to 51% attacks, but from economic infeasibility, making attacks irrational." — Dr. Stuart Haber, Blockchain Researcher.
Takeaway 2: The "Rent-a-Riot" Economy for Smaller Networks
If Bitcoin is a fortress, smaller blockchains are often gated communities with a single, sleepy guard. For these networks, attackers don’t need to buy billions in hardware; they can simply rent a riot.
Marketplaces like NiceHash allow malicious actors to lease massive amounts of hashing power for just a few hours. This is particularly lethal for "ASIC-resistant" networks or smaller Bitcoin forks. Since these chains rely on hardware that is widely available (like consumer GPUs), an attacker can rent enough power to overwhelm the network for a fraction of the value they intend to steal. In this "Rent-a-Riot" economy, the cost of the heist is frequently lower than the prize, making the attack a logical business decision.
Takeaway 3: The Ghost in the Machine (Mechanics of Private Mining)
A 51% attack isn't a "hack" in the traditional sense; no private keys are cracked, and no wallets are drained via software bugs. Instead, the attacker mines a "private" version of the truth in total silence.
Accumulation: The attacker acquires 51% of the network's hashing or staking power.
Partitioning: The attacker stops communicating with the rest of the network. They begin mining a "shadow" version of the blockchain that they keep hidden from the public.
Accelerated Extension: Math takes over. Because the attacker has 51% of the power and the legitimate network has 49%, the shadow chain grows faster. While the public network mines 10 blocks, the attacker mines roughly 10.4 blocks.
Forced Reorganization: Once the shadow chain is longer, the attacker broadcasts it to the world. Under the Longest Chain Rule (or "Most Work" rule), all nodes are forced to discard the public history and adopt the shadow chain. The legitimate chain is "orphaned," and its history is erased.
Double Spending: During the split, the attacker sends coins to an exchange on the public chain and cashes out. After the reorganization, that original deposit is wiped from history. The attacker now has the cash and the original coins back in their wallet.
Takeaway 4: Real Casualties in a "Theoretical" War
This isn't an academic exercise. The "Ghost" has appeared multiple times, leaving a trail of broken reputations and empty ledgers.
Bitcoin Gold (May 2018): In a sophisticated campaign, attackers successfully executed a $18 million double-spend targeting the Bitfinex exchange.
Ethereum Classic (August 2020): ETC suffered multiple reorganizations in a single month. The exchange Gate.io reported losses of $5.6 million as history was repeatedly rewritten.
Vertcoin (December 2018): A smaller-scale but successful $100,000 attack proved that even modest targets are at risk.
Once a network’s immutability is proven to be a myth, user confidence rarely recovers. The market value often collapses, leaving the blockchain a "ghost town" of its former self.
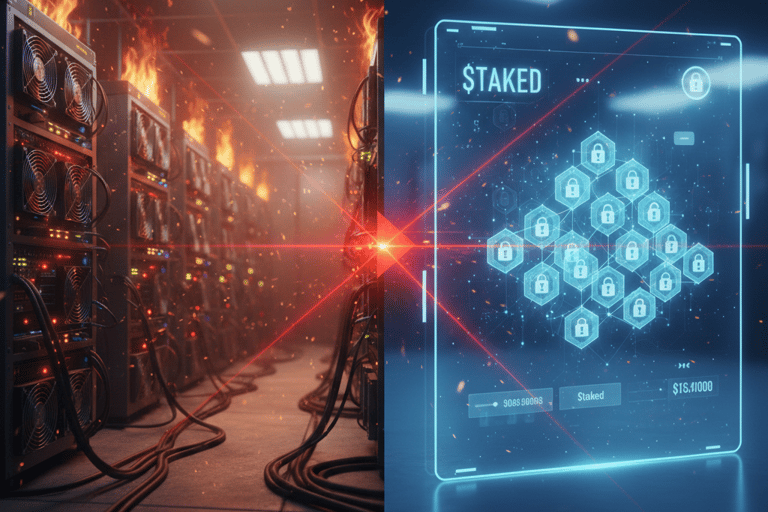
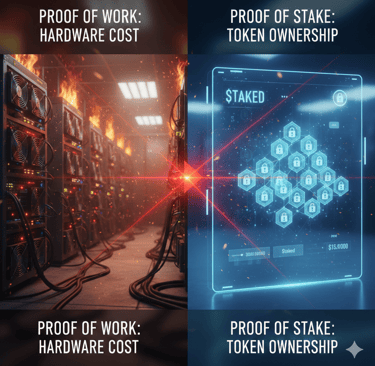
Takeaway 5: Proof of Stake as a "Capitalist" Defense
To close the "Rent-a-Riot" loophole, the industry is pivoting from hardware-based Proof of Work to capital-based Proof of Stake (PoS). This shifts the battlefield from mining rigs to the token supply itself.
In a PoS network like the post-Merge Ethereum, an attacker cannot simply rent GPUs; they must own and stake a majority of the circulating currency. To attack Ethereum today would require an investment of tens of billions of dollars. Crucially, PoS introduces "Slashing": if the network detects a 51% reorganization attempt, the attacker's entire multi-billion dollar stake is "burned"—destroyed by the protocol. This turns a heist into a kamikaze mission where the cost of the attack is guaranteed to exceed the rewards.
Conclusion: The Nuclear Option and the Future of Trust
Blockchain security is a game of incentives. It relies on the assumption that it is always more profitable to be honest than to be a thief. But when the math fails, there is a final, human line of defense: The Nuclear Option.
Through community governance, users can decide to trigger a Hard Fork. This is a manual override where the community collectively agrees to ignore the "mathematical" majority chain and move to a new version of the ledger where the attack never happened.
It leaves us with a haunting question: If the "truth" on a blockchain is simply whatever the majority says it is—or whatever a community decides to fork into existence—can we ever achieve absolute security? Or is "immutable" trust just a human agreement in a high-tech disguise?
Frequently Asked Questions
What is a 51% attack? A 51% attack occurs when a single entity or coordinated group controls more than half of a blockchain network's consensus power (hash rate in Proof of Work or tokens in Proof of Stake). This control allows them to manipulate the order of transactions and reverse their own recent payments.
Why is a 51% attack dangerous? It destroys the fundamental trust in the network. Attackers can "double-spend" their coins, reverse finalized transactions, and prevent others from completing transfers. While they cannot steal your private keys or take coins from your wallet, they can rewrite the history of their own spending, often leading to a collapse in the network's market value.
Can Proof of Stake prevent 51% attacks? While not immune, PoS makes attacks significantly more expensive. Attackers must own a majority of the circulating currency rather than just renting hardware. Furthermore, "slashing" protocols allow the network to financially penalize malicious actors by destroying their multi-billion dollar investment if they attempt to manipulate the ledger.